ARC Leadership Forum, 2025: CISA expert offers risk mitigation tips in the ongoing Salt Typhoon telecom hack, worst in U.S. history, with other industrial cybersecurity advice.
Salt Typhoon insights
- Understand what Salt Typhoon hack is, impact and CISA’s mitigation suggestions.
- Review CISA cybersecurity roles and the 16 critical infrastructure sections.
- Assess what CISA resources you or your organization could to lower cybersecurity risk.
Salt Typhoon telecommunication hack is an ongoing exploitation of AT&T, Lumen, T-Mobile, Verizon and other networks, from a state-sponsored hacking group in October 2024, explained as the worst telecom hack in U.S. history by the Cybersecurity and Infrastructure Security Agency (CISA) at the 2025 ARC Leadership Forum by ARC Advisory Group. The hack gained access to millions of U.S. call detail records, who talk to, how often, at what times and location data, including highly sensitive law enforcement intelligence and law enforcement data, according to Neal Arnold, cybersecurity advisor – law enforcement liaison, Region IV, Cybersecurity advisor program, CISA.
Arnold (see Figure 1) said Salt Typhoon is not a traditional compromise because no confirmation has been given that Salt Typhoon has been evicted from compromised networks. Arnold said Salt Typhoon has embedded itself in older, aging network equipment and in niche networking that’s difficult to detect. In addition:
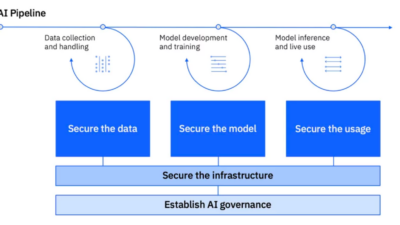
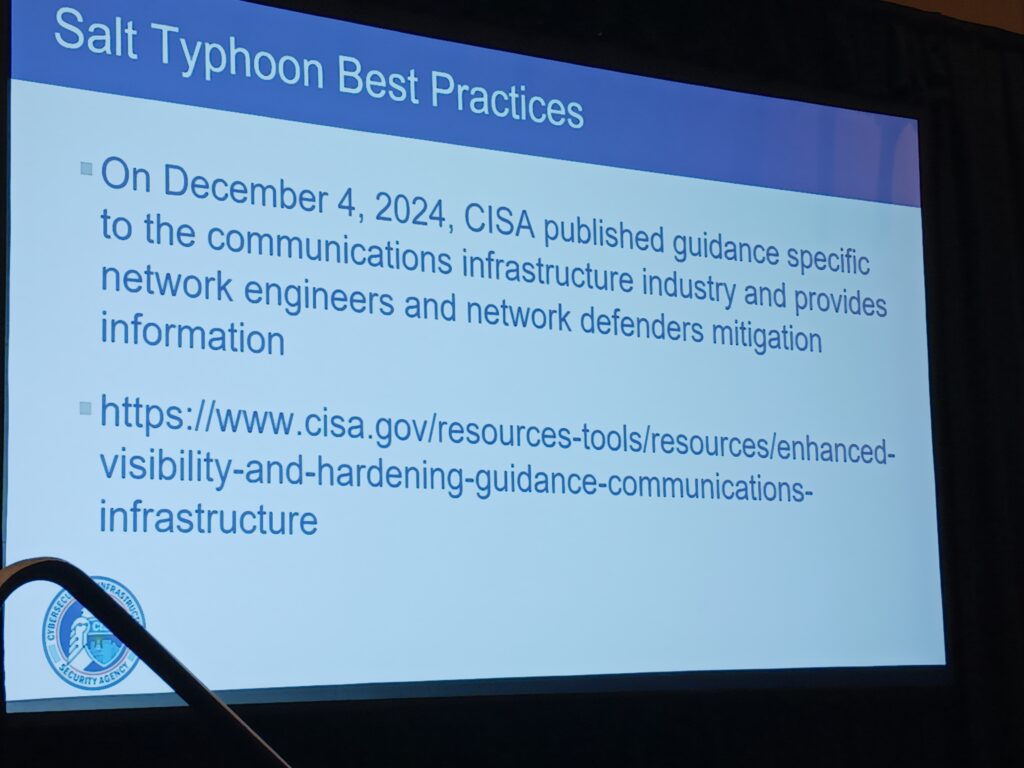
- On Dec. 4, 2024, CISA published guidance specific to the communication infrastructure, providing network engineers and network defenders mitigation information (see Figure 2).
- CISA and the FBI urged Americans to use fully encrypted text messaging apps to minimize chances of sharing information with the Peoples Republic of China (PRC).
- If possible, conduct business over Microsoft Teams, Webex or other similar platforms.
- The most sensitive conversations should be in person, including sensitive critical infrastructure and manufacturing-related intellectual property information.
Arnold’s presentation, “Cybersecurity threat landscape: Securing critical infrastructure,” covered industrial cybersecurity from the CISA perspective. He explained that CISA will reach out when operational technology (OT) products have a vulnerability and are being exploited. As with any contact, he recommends verifying and contacting CISA back, though perhaps not via email, which may also be compromised, he said.
What does CISA do?
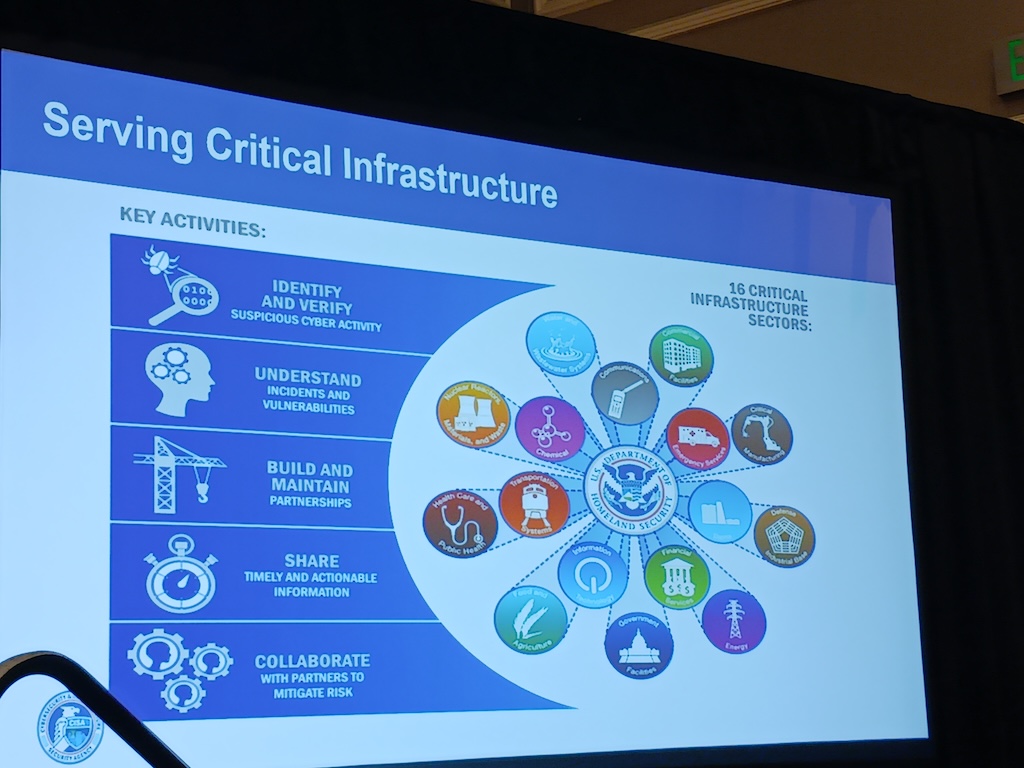
The five key CISA activities across 16 critical infrastructure sections (Figure 3) are:
1. Identify and verify suspicious cyber activity.
2. Understand incidents and vulnerabilities.
3. Build and maintain partnerships.
4. Share timely and actionable information.
5. Collaborate with partners to mitigate risk.
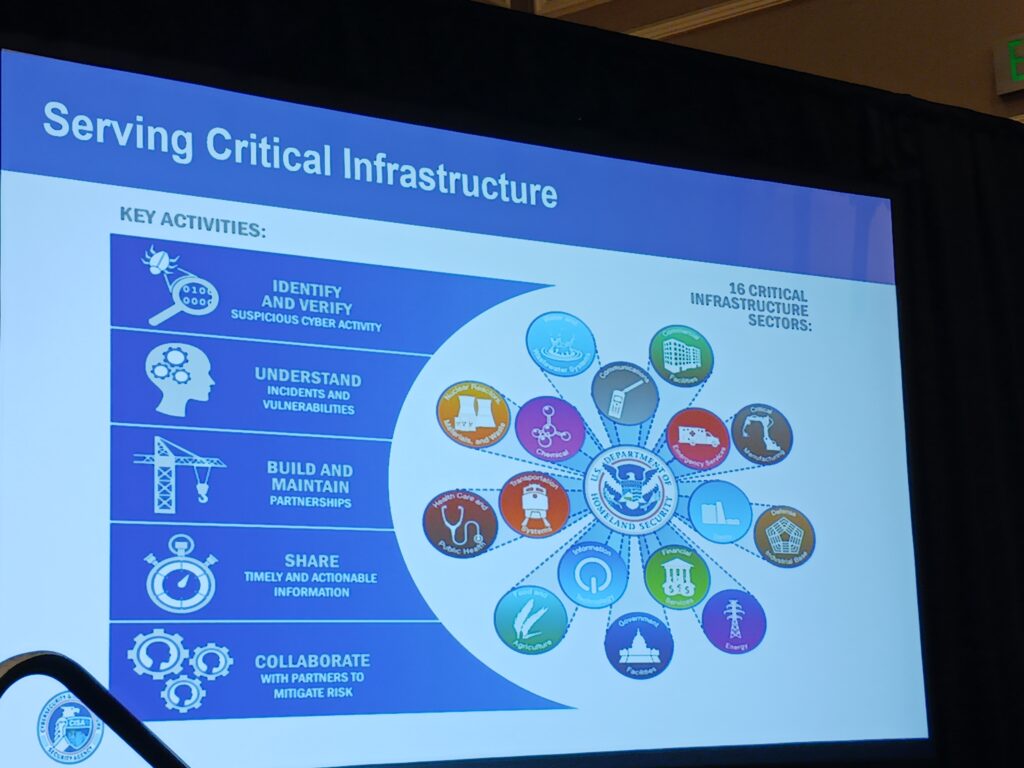
What are the 16 critical infrastructure sections?
Many of the 16 critical infrastructure sections use automation, control and instrumentation.
1. Chemical
2. Commercial facilities
3. Communications
4. Critical manufacturing
5. Dams
6. Defense industrial base
7. Emergency facilities
8. Energy
9. Financial services
10. Food and agriculture
11. Government facilities
12. Health care and public health
13. Information technology
14. Nuclear reactors, materials and waste
15. Transportation systems
16. Water and wastewater systems
Industrial cybersecurity threats, advanced threats
Cyber threat factors include ransomware; sophistication phishing; internet of things (IoT) malware and vulnerabilities; data theft, fraud and breaches; supply chain attacks; teleworking; insider threats; lack of protection and policies; and advanced persistent threats (APTs).
Supply chain threats include:
- Software service providers and outside contractors through exploitation of smaller, typically less-secure companies with access to or credentials for the networks of larger corporations.
- Mergers and acquisitions: Inheriting the (lack of) security from smaller companies.
- Physical components: Hidden “backdoors” embedded in software or hardware.
- Network services: Do you know the route your digital traffic takes from one point to the next?
- IoT may prioritize time to market over security.
Advanced threats include:
- Social engineering: Scattered spider, SIM swapping, account takeovers, reset passwords and multi-factory authentication (MFA) removal, data exfiltration, extortion and ransomware.
- Artificial intelligence (AI), a program that can sense, reason, act and adapt: Machine learning (ML), algorithms whose performance improve when exposed to more data over time; deep learning, an ML subset where multilayered neural networks learn from vast amounts of data; large language models; generative AI; deepfakes; and artificial general intelligence.
Critical infrastructure and industrial cybersecurity hygiene, procedures
Basic cybersecurity hygiene is highly recommended, such as MFA, strong passwords (long, unique and randomly generated), prompt software updates (automatically, if possible), train to recognize and report phishing (one click can install malware), Arnold said.
Be suspicious of emails from unknown senders, do not provide personal or corporate sensitive information requested via email, do not use contact information from the email or phone request. Contact the organizer directly to verify. Do not send personal information on the internet without checking website security first.
If you have been affected, report it immediately, including proper points of contact in an organization; prevent the spread by isolating the infected computers and systems. Disconnect from the internet, but do not turn off the machine. Try to identify the type of ransomware to help understand what you are working with. Work with cybersecurity professional trained in resolving these issues. Recover your data from your backups after you test the backups to ensure the data on the backups is safe to restore.
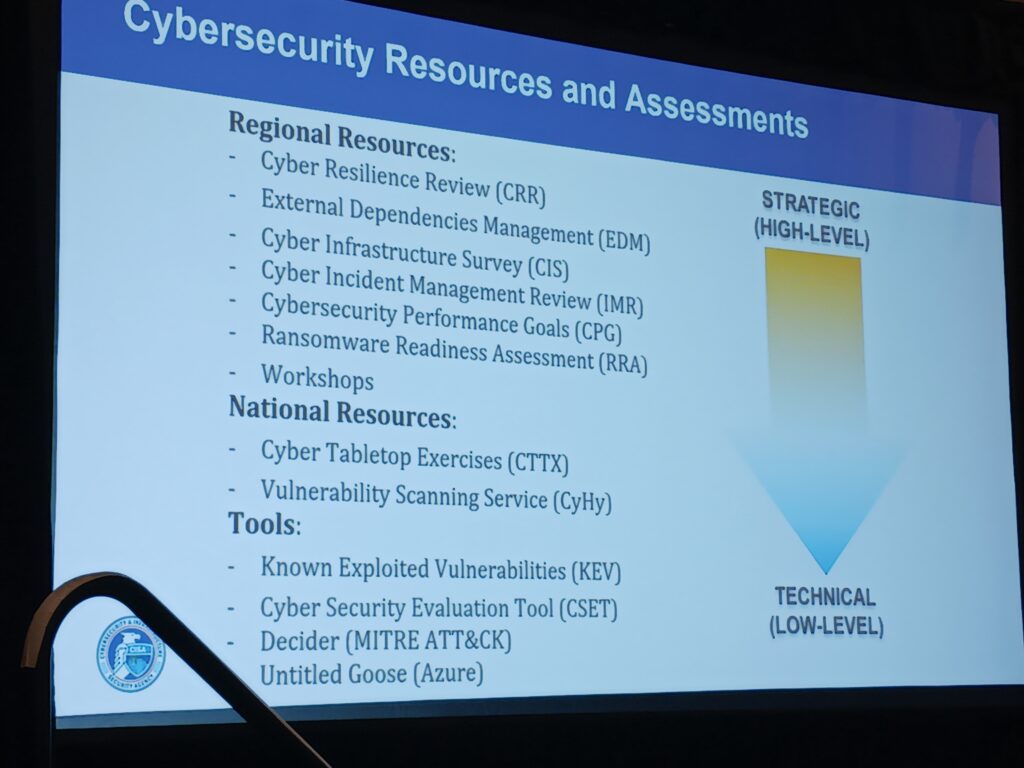
Only about 20% of critical infrastructure cybersecurity incidents are reported. There are no mandates, but Arnold said mandates are likely in the future, adding that reporting to CISA is confidential and protected against litigation, sunshine laws and civil litigation. CISA cyber services are paid through tax dollars and should be used when appropriate, including assessments, vulnerability scanning and hygiene. Better to have us do a CISA Cyber Hygiene Assessment than to have a hacker do so (Figure 4). CISA also offers physical security assessments, he said. Results from assessments can help with grants and funding for cybersecurity upgrades.
Mark T. Hoske, editor-in-chief, Control Engineering, WTWH Media, [email protected].
CONSIDER THIS
Are you following government-available guidance on critical infrastructure cybersecurity?
ONLINE
Read more on industrial cybersecurity from Control Engineering.