Manufacturing and other industrial sectors are among the most targeted by cybercriminals and shoulder some of the highest costs resulting from a data breach. Right now — as hybrid cloud, generative AI and quantum computing upend the cybersecurity paradigm — comprehensive data security is more important than ever.
Cybersecurity insights
- Comprehensive data security is more important than ever as hybrid cloud, generative AI and quantum computing emerge.
- Securing data is important since technicians, machines, edge devices and IoT tools have varying degrees of access to data across multiple clouds.
- To mitigate data security risks, industrial engineers need “crypto agility,” the ability to quickly switch between different encryption mechanisms that protect sensitive data.
Factory floors, plant control rooms and other industrial engineering settings are growing smarter each day, highlighting the need for more intensive data security. Industrial engineers are eager to enhance their control systems and operational technology with the latest digital capabilities, like generative AI.
Smarter settings mean more efficiency, insights and control — all enabled by more data. But as industrial settings grow more data rich, critical data is often left unprotected. For the third year in a row, the IBM X-Force Threat Intelligence Report ranked manufacturing as the most-attacked industry by cybercriminals.
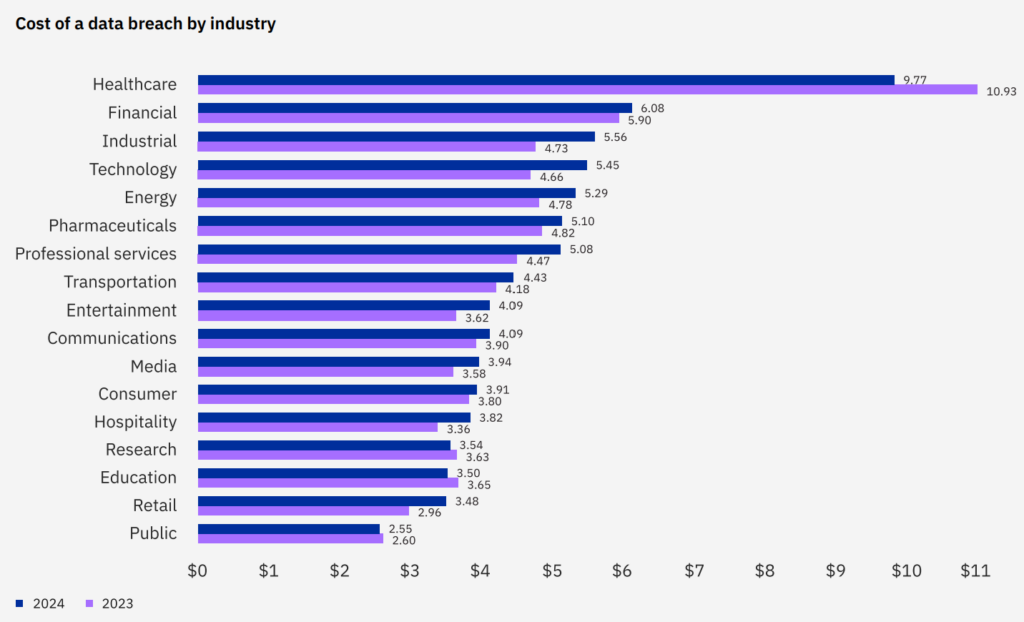
And cyberattacks are just one issue: There’s also the possibility of insider threats, human error and compliance failures. These carry a significant price tag. Industrial organizations see some of the highest data breach costs — an average of $5.6 million — according to IBM’s annual Cost of a Data Breach Report.
Data security in a sensitive sector
This shouldn’t be surprising. The industrial sector has always been an attractive target for bad actors due to its coveted IP like proprietary designs and sensitivity to downtime. For example, automakers can lose over $20,000 per minute of unplanned downtime.
Nor should these trends be a reason to eschew emerging technologies. Innovation has always been the lifeblood of industrial engineering.
However, these trends make clear the importance of data security in industrial engineering. Especially at this moment in time, as compliance grows more complex and as three major digital transformations — hybrid cloud, generative AI and quantum computing — upend the traditional data security paradigm.
Amid these rapid changes, cybersecurity professionals in the industrial sector should approach data security with three key priorities: laying a strong foundation; meeting emerging risks; and preparing for future risks.
Laying a strong foundation: data security basics
While the data security paradigm is transforming, there are still long-standing best practices that security professionals should always employ. These are the nuts-and-bolts of data security that date back to the days when data was only stored in mainframes on-premises.
Data security professionals should have robust answers to a few important questions: Do you know where your most sensitive data is stored? Is that data being actively monitored? Do you have a plan in place — e.g. containment, notification, improvement — for when a data breach occurs? It’s when a breach occurs, not if. The industrial sector should anticipate the worst-case scenario. The IBM X-Force Threat Intelligence Report also found data theft and data leakage to be the most common incidents.
Protecting data throughout its full lifecycle — from collection to storage and processing to disposal – is fundamental. This means being diligent about discovering and protecting data and then analyzing and responding to risks and threats in real time.
Comprehensive Identity and Access Management (IAM) is also a requirement. Determining who or what can access your systems — and data — is especially important in the industrial sector, where a vast array of technicians, machines, edge devices and IoT tools have varying degrees of access to data across multiple clouds.
Hybrid cloud adoption and generative AI proliferation
Once industrial engineers have a strong data security foundation to build upon, they can expand their work to address newer risks and threats. Right now, those surfaces are hybrid cloud and AI — particularly generative AI.
The days of data being stored solely on premises are gone due to hybrid cloud and AI transformations. Industrial engineers’ data now lives across multiple clouds and within large language models. This has major upsides, empowering engineers to optimize supply chains, predict asset maintenance needs and enhance quality control.
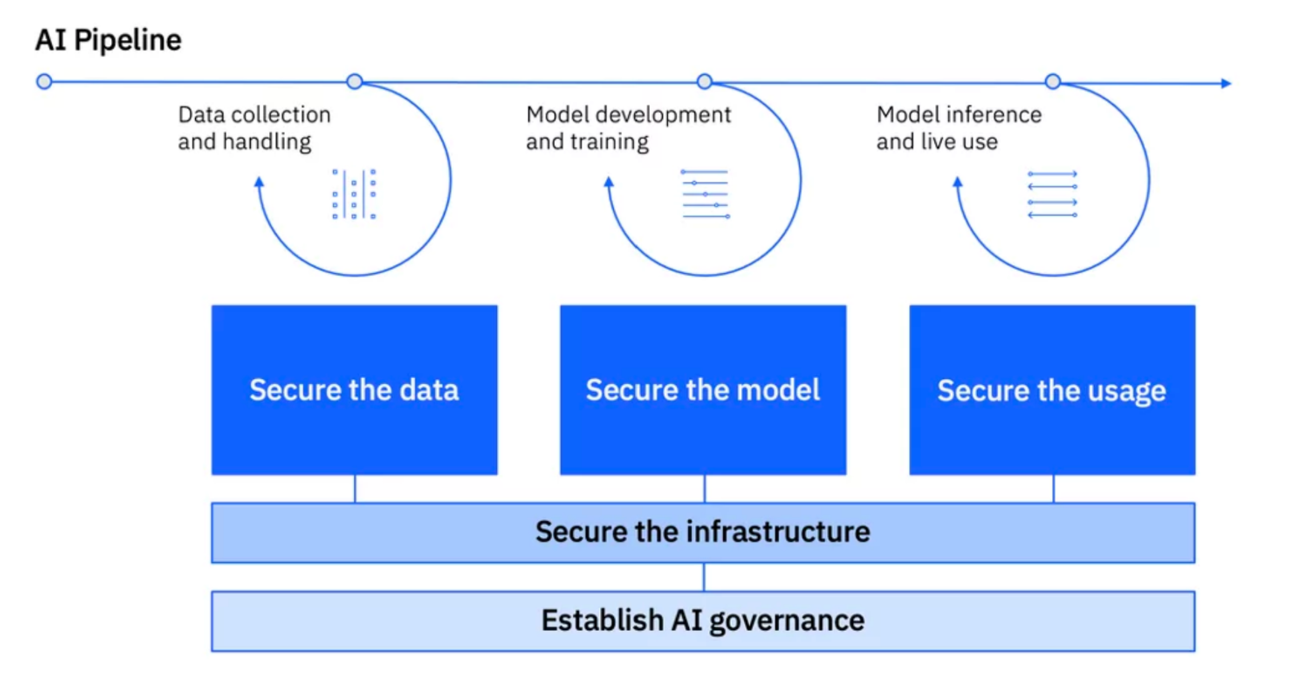
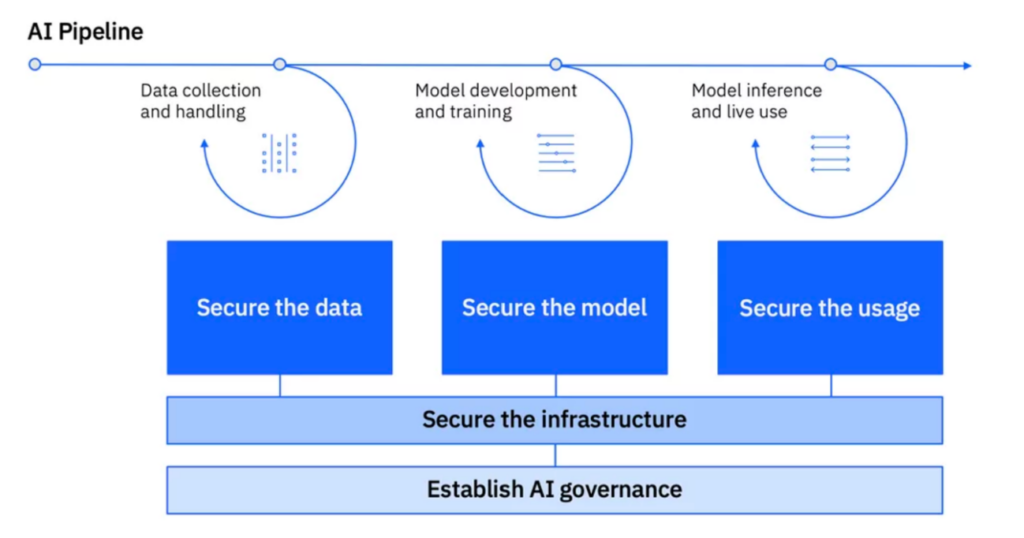
These upsides also come with risks, however. It’s easier than ever to lose sight of where data is stored, who has access and how it is protected. “Shadow data” like this significantly escalates the likelihood of a breach. Likewise, the use of generative AI introduces more potential attack surfaces: the training data, the model and the model’s usage. Generative AI like large language models also presents entirely novel vulnerabilities, like prompt engineering, jailbreaks and “shadow AI.” Shadow AI are unsanctioned models operating within a business’s digital ecosystem, often introduced by negligent staff, that elude governance. Recent research by IBM revealed that only 24% of current generative AI projects are being secured. If industrial engineers are using generative AI, they must protect the entire AI pipeline: secure the data, secure the models and secure the usage.
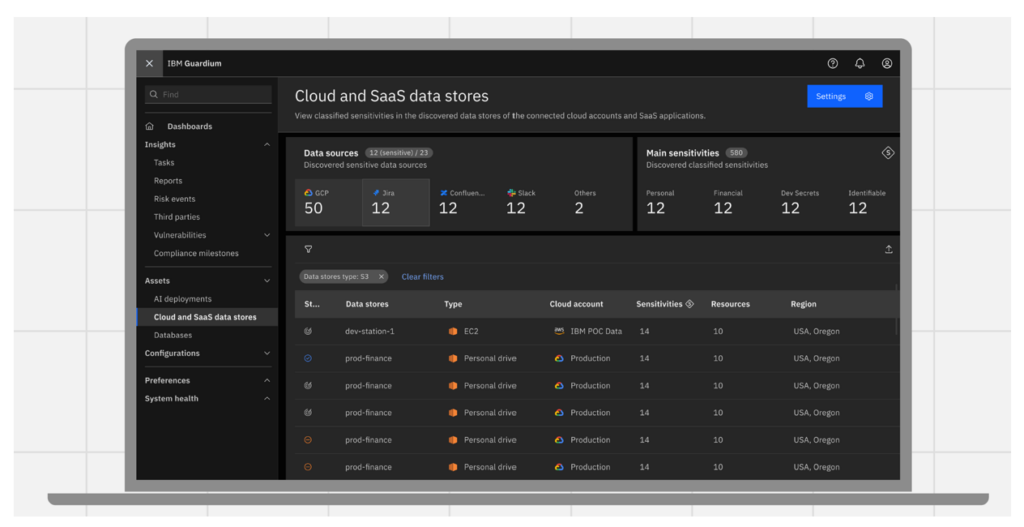
How should security professionals in the industrial sector pursue this type of comprehensive protection? The wrong way to go about this is with a patchwork of isolated point solutions: one piece of software for this surface area, another piece of software for that surface area. A fragmented approach inevitably leads to silos, limited visibility and breaches. Instead, security professionals need unified controls that grant visibility across teams and surface areas. The need for this unified experience was a guiding force behind IBM’s newest data security software. We heard repeatedly from security professionals in the industrial sector and others that they need a single package with multiple capabilities: data monitoring and compliance, data and AI security posture management, data detection and response and cryptography management.
Preparing for future risks: quantum-safe cryptography
While cybersecurity professionals acclimate to hybrid cloud and generative AI impacts on data security, another technological transformation is just over the horizon: quantum computing.
Quantum computing carries immense potential in industrial engineering, like discovering new materials and tackling other complex problems that classical computers struggle with. But bad actors with quantum-powered technology may one day be able to break today’s encryption. Experts predict that quantum computing could challenge present-day encryption by the end of the current decade.
This scenario presents current dangers, too. The notion of “harvest now, decrypt later” can place industrial organizations’ IP and other sensitive data at risk right now. Bad actors could potentially harvest encrypted data now and years later decrypt it using cryptographically relevant quantum-powered attacks. This can pose a real problem in industrial engineering, where proprietary designs and trade secrets have long shelf lives.
To mitigate these risks, industrial engineers need “crypto agility,” the ability to quickly switch between different encryption mechanisms that protect sensitive data. This requires visibility into all encrypted assets and also the ability to transition from traditional encryption techniques to newer, post-quantum cryptography like the standards recently set by NIST.
Prioritizing data security in industrial networks
Data security should always be a top priority, especially in industrial engineering. The field’s innate qualities — like its complexity and its importance — mean security professionals need a comprehensive and proactive approach to the data security trade. By laying a strong foundation, expanding to protect emerging risks and then finally preparing for risks on the horizon, security professionals in industrial engineering can ensure their critical work and innovations remain safe.
Akiba Saeedi is the vice president of product management data security and cloud/service providers with IBM. Edited by Sheri Kasprzak, managing editor, Automation & Controls, WTWH Media, [email protected].



